Hacking a X-RAY Machine with WHIDelite & EvilCrowRF

The first thing striked my curiosity, even before purchasing it, was its remote. Which were the odds that the little teeny-tiny remote was just using an ASK/OOK modulation with no replay-attack protection whatsoever?! Very high of course.
Nonetheless, I ordered it anyway and used it as an excuse to try again my WHIDelite and the new toy that Joel sent me over (EvilCrowRF).
But first let’s follow a more-systematic approach with HackRF and URH:
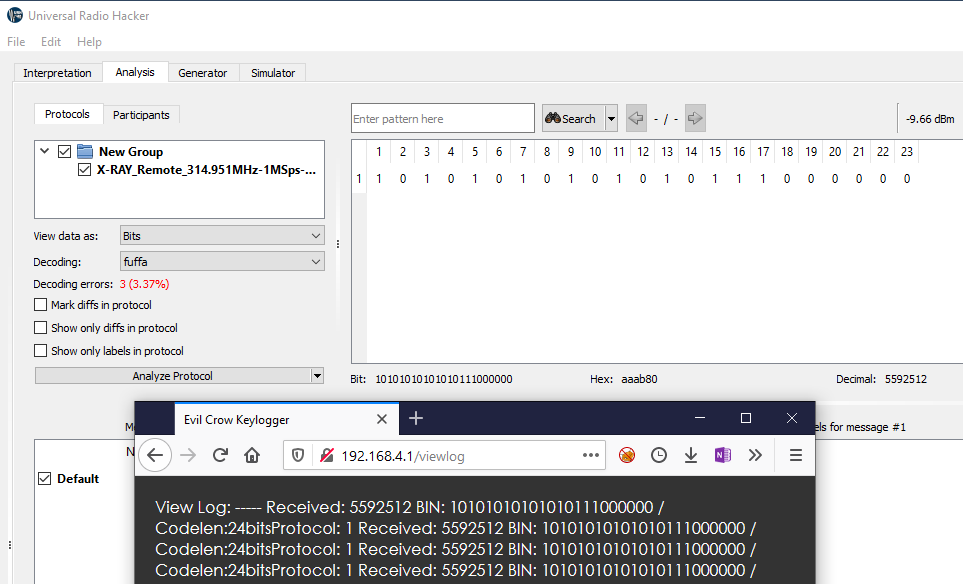
- Frequency is confirmed being set around 315MHz

- After recording a packet we can confirm that is using an ASK/OOK modulation.

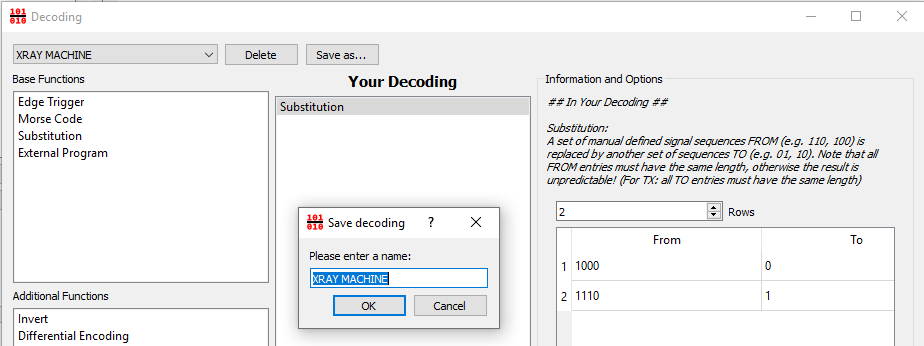
- After creating a simple substitution decoding, we get exactly the same values that both EvilCrowRF & WHIDelite showed during the initial tests.
☢ This crap is absolutely NOT secure! ☢

Just
for the sake of confirmation, I did replay the packet with both HackRF,
WHIDelite & EvilCrowRF. In all cases, the forged packet was
successfully received and decoded by the unit, which fired X-RAYs like
it was a Marie Curie’s party
WHID's Trainings
The Offensive Hardware Hacking Training is a Self-Paced training including Videos, a printed Workbook and a cool Hardware Hacking Kit. And… you get everything shipped home Worldwide!
For more info… ➡ https://www.whid.ninja/store
